Summarize this blog post with:
HyperText Transfer Protocol Secure (HTTPS) is an encrypted version of HTTP, the protocol your browser uses to load web pages. HTTPS protects the data flowing between a visitor’s browser and your server so attackers cannot intercept, read, or alter it.
Any website that displays a lock icon in the browser address bar is using HTTPS.
![[Screenshot: browser address bar showing the lock icon on a live HTTPS site]](https://www.datocms-assets.com/164164/1776444368-blobid1.png)
If your site still runs on HTTP, you are sending every form submission, login credential, and page request in plain text. Anyone sitting on the same network—a coffee shop, an airport, a compromised router—can read that data. HTTPS solves this by encrypting the connection end to end.
But security is only half the story. Google confirmed HTTPS as a ranking signal back in 2014. And as AI search engines like ChatGPT, Perplexity, Gemini, and Copilot grow in influence, the trust signals associated with HTTPS extend to whether your content gets cited in AI-generated answers.
In this article, you’ll learn what HTTPS is, why it matters for both traditional search and AI search engines, how TLS certificates work, how to set up HTTPS on your site, and how to find and fix the most common migration mistakes that hurt your rankings.
Table of Contents
HTTP vs. HTTPS: Understanding the Basics
To understand why HTTPS matters, you first need to understand what happens without it.
When you type a URL into your browser, the browser sends an HTTP request to the server. The server responds with the page content. This exchange happens in plain text.
That means anyone between the browser and the server—your internet service provider, a rogue WiFi hotspot operator, a hacker on the same network—can see everything. They can read your passwords. They can inject malicious code into the page. They can redirect you to a fake version of the site.
![[Screenshot: simple diagram showing HTTP request/response with an attacker intercepting data in the middle]](https://www.datocms-assets.com/164164/1776444373-blobid2.png)
HTTPS stops all of this by adding a layer of encryption. When a browser connects to an HTTPS site, the two sides perform a “handshake” that establishes a shared encryption key. From that point on, every piece of data sent between browser and server is scrambled. Even if someone intercepts it, they see random characters instead of credit card numbers or login credentials.
Think of it like sending a package in an indestructible locked box. Only the sender and receiver know the combination. If someone grabs the box in transit, they cannot open it.
HTTPS relies on TLS (Transport Layer Security) to handle this encryption. You may also hear it called SSL—that is the older name for the same technology. In practice, everyone says “SSL certificate” even though TLS replaced SSL years ago.
Attacks HTTPS Prevents
Without HTTPS, your site is exposed to several well-documented attack types:
Man-in-the-middle (MITM): An attacker positions themselves between the browser and the server, intercepting and potentially altering communication in both directions. This is the most common attack on unsecured networks.
Session hijacking: When session cookies are sent over an unencrypted connection, an attacker can steal them and impersonate the user. This is how accounts get compromised on public WiFi.
SSL stripping: An attacker downgrades a connection from HTTPS to HTTP without the user noticing. The browser shows no lock icon, but most users do not check. HSTS (which we cover later) specifically prevents this.
Content injection: Without encryption, anyone on the network path can inject ads, tracking scripts, or malware into the page content before it reaches the browser. Some ISPs have been caught doing this to inject their own advertisements.
Credential theft: Any login form submitted over HTTP sends the username and password in plain text. Network sniffing tools like Wireshark can capture these credentials in seconds.
HTTP/2, HTTP/3, and Why HTTPS Is a Prerequisite
One detail that often gets overlooked: HTTPS is not just about security. It is also the gateway to faster page loads.
HTTP/2 is the modern version of the HTTP protocol. It allows browsers to load multiple resources simultaneously over a single connection, compresses headers, and supports server push. The result is noticeably faster page loads. But HTTP/2 only works over HTTPS. No encryption, no HTTP/2.
HTTP/3 takes this even further. It replaces TCP with a protocol called QUIC, which establishes connections faster (zero round-trip handshakes in some cases), handles packet loss more gracefully, and performs better on mobile networks. Like HTTP/2, HTTP/3 requires HTTPS. As of 2025, HTTP/3 accounts for roughly 35% of global web traffic.
So when people ask whether HTTPS slows down their site because of encryption overhead, the answer is the opposite. HTTPS enables the protocols that make your site faster.
How TLS Certificates Work
To enable HTTPS on your site, you need a TLS certificate installed on your server. This certificate does two things: it proves your server is who it claims to be, and it provides the encryption keys needed to secure the connection.
TLS certificates are issued by Certificate Authorities (CAs)—trusted third parties that verify your identity before issuing the certificate. Browsers come pre-loaded with a list of CAs they trust. If your certificate was issued by a trusted CA, the browser shows the lock icon. If not, the browser shows a warning.
You can inspect any site’s TLS certificate by clicking the lock icon in your browser’s address bar.
![[Screenshot: clicking the lock icon and viewing certificate details in Chrome, showing the “Issued to” and “Valid from/to” fields]](https://www.datocms-assets.com/164164/1776444374-blobid3.png)
TLS Versions: Why 1.3 Matters
Not all TLS is equal. The version your server uses directly affects both security and performance.
TLS 1.3 (released 2018): The current standard. It removes outdated cryptographic algorithms, reduces the handshake from two round trips to one (or even zero with 0-RTT resumption), and is significantly faster than older versions. If your hosting provider supports TLS 1.3, enable it.
TLS 1.2 (released 2008): Still acceptable and widely supported. Most servers run TLS 1.2 as a fallback for older clients. This is fine as a secondary option.
TLS 1.0 and 1.1: Deprecated. Major browsers dropped support in 2020. Microsoft officially deprecated these versions in early 2026. If your server still offers TLS 1.0 or 1.1, disable them immediately. They have known vulnerabilities.
The best practice is to configure your server for TLS 1.3 with a TLS 1.2 fallback. You can test your configuration for free using Mozilla Observatory or Qualys SSL Labs.
![[Screenshot: Qualys SSL Labs test result showing an A+ rating with TLS 1.3 enabled]](https://www.datocms-assets.com/164164/1776444378-blobid4.png)
DV, OV, and EV: Certificate Validation Levels
TLS certificates come in three validation levels. The level you need depends on what your site does.
Domain Validation (DV): The CA verifies only that you control the domain. This is the most basic level. It is free through services like Let’s Encrypt, which holds roughly 64% market share among certificate authorities. DV certificates are fine for blogs, informational sites, and most business websites.
Organization Validation (OV): The CA verifies both domain ownership and the legal existence of the organization. This adds a layer of trust—visitors can click the lock icon and see which company owns the site. OV certificates typically cost $50–200 per year.
Extended Validation (EV): The most rigorous level. The CA performs detailed background checks on the organization. EV certificates used to trigger a green address bar in browsers, but most browsers stopped this visual indicator in 2019. They still show the organization name when you click the lock icon. EV certificates cost $100–500 per year.
For most sites, a DV certificate from Let’s Encrypt is sufficient. If your site handles payments or sensitive personal data, consider upgrading to OV or EV.
|
Feature |
DV |
OV |
EV |
|---|---|---|---|
|
Validates domain ownership |
Yes |
Yes |
Yes |
|
Validates organization identity |
No |
Yes |
Yes (rigorous) |
|
Typical cost |
Free |
$50–200/year |
$100–500/year |
|
Issuance speed |
Minutes |
1–3 days |
1–2 weeks |
|
Best for |
Blogs, small sites |
Business sites |
E-commerce, finance |
Wildcard and SAN Certificates
If you run multiple subdomains (blog.example.com, shop.example.com, docs.example.com), managing individual certificates for each gets tedious. Two certificate types solve this.
Wildcard certificates cover an unlimited number of subdomains under one domain. A wildcard for *.example.com would cover blog.example.com, shop.example.com, and any other subdomain you add in the future.
SAN (Subject Alternative Name) certificates cover multiple specific domains and subdomains. Unlike wildcards, SAN certificates can cover entirely different domain names—for example, example.com, example.net, and blog.example.com on a single certificate.
Most hosting providers and CDNs handle certificate management automatically, but if you manage certificates manually, understanding these options will save you time and money.
How HTTPS Helps SEO
Every benefit of HTTPS connects back to search performance in some way. Here is how.
HTTPS Is a Google Ranking Signal
Google announced HTTPS as a ranking signal in 2014. It is a lightweight factor—more of a tiebreaker than a game-changer. If two pages are equal in every other way, the HTTPS page will outrank the HTTP page.
But the real impact goes beyond rankings. Google Chrome, which holds over 65% of global browser market share, displays a “Not secure” warning on any HTTP page. This warning directly affects user behavior.
![[Screenshot: Chrome “Not secure” warning displayed in the address bar of an HTTP site]](https://www.datocms-assets.com/164164/1776444379-blobid5.png)
When visitors see that warning, many of them leave immediately. That increases your bounce rate and decreases dwell time—both signals that correlate with lower rankings.
Chrome’s HTTPS-by-default rollout: Starting in October 2026 (Chrome 154), Chrome will automatically attempt HTTPS connections first and display an interstitial warning before loading any HTTP site. The rollout begins in April 2026 for Enhanced Safe Browsing users. If your site still uses HTTP, this change will actively drive visitors away.
HTTPS Preserves Referral Data
If your site runs on HTTP and you use analytics tools like Google Analytics, you have a blind spot. When a visitor clicks a link from an HTTPS site to your HTTP site, the referral data is stripped. That traffic shows up as “direct” in your analytics—not as a referral from the site that linked to you.
Since over 89% of the web now runs on HTTPS, most of your inbound links come from HTTPS sites. If your own site is HTTP, you cannot see where your traffic actually comes from. This makes it impossible to identify your best link building opportunities or understand which content is earning referral traffic.
Switching to HTTPS fixes this. Your analytics will accurately attribute traffic to its source.
HTTPS Enables Faster Page Loads
As covered earlier, HTTPS is the prerequisite for HTTP/2 and HTTP/3. These protocols deliver measurably faster page loads through multiplexing, header compression, and improved connection handling.
Google has explicitly stated that page speed is a lightweight ranking factor, similar in weight to HTTPS itself. By enabling HTTPS, you unlock the speed improvements that come with modern protocols—which then feed back into better search performance.
HTTPS Builds Trust for Both Users and Search Engines
The trust dimension of HTTPS extends beyond the lock icon. Google’s E-E-A-T guidelines (Experience, Expertise, Authoritativeness, Trustworthiness) emphasize trust as a core ranking consideration. A site serving pages over HTTP sends a negative trust signal to both users and search engine quality raters.
This trust signal matters for technical SEO audits too. When you audit a site’s technical health, HTTPS status is typically one of the first checkboxes.
How HTTPS Affects AI Search Visibility
Search is expanding. Alongside traditional organic results, AI engines like ChatGPT, Perplexity, Gemini, and Microsoft Copilot are now answering user questions directly—and citing sources in their responses. This creates a new organic channel that sits alongside traditional SEO, not in place of it.
HTTPS plays a role in this new channel for several reasons.
AI Crawlers Require HTTPS
AI search engines rely on web crawlers to build the knowledge bases they draw from when generating answers. These crawlers—GPTBot (OpenAI), ClaudeBot (Anthropic), PerplexityBot, Google-Extended—follow the same rules as Googlebot. They need to crawl your pages to include your content in their training data and real-time search results.
If your site serves pages over HTTP, some AI crawlers may deprioritize or skip it entirely. Crawlers are increasingly configured to prefer HTTPS sources because encrypted connections are more reliable and harder to tamper with.
Trust Signals Influence AI Citations
When an AI engine generates an answer and decides which sources to cite, it evaluates trust signals. These include domain authority, content quality, freshness, and yes—whether the site uses HTTPS.
A site serving content over HTTP sends a low-trust signal. AI models are trained to prefer authoritative, well-maintained sources. Running on HTTP in 2026 suggests the site is not well-maintained—which makes it less likely to be cited.
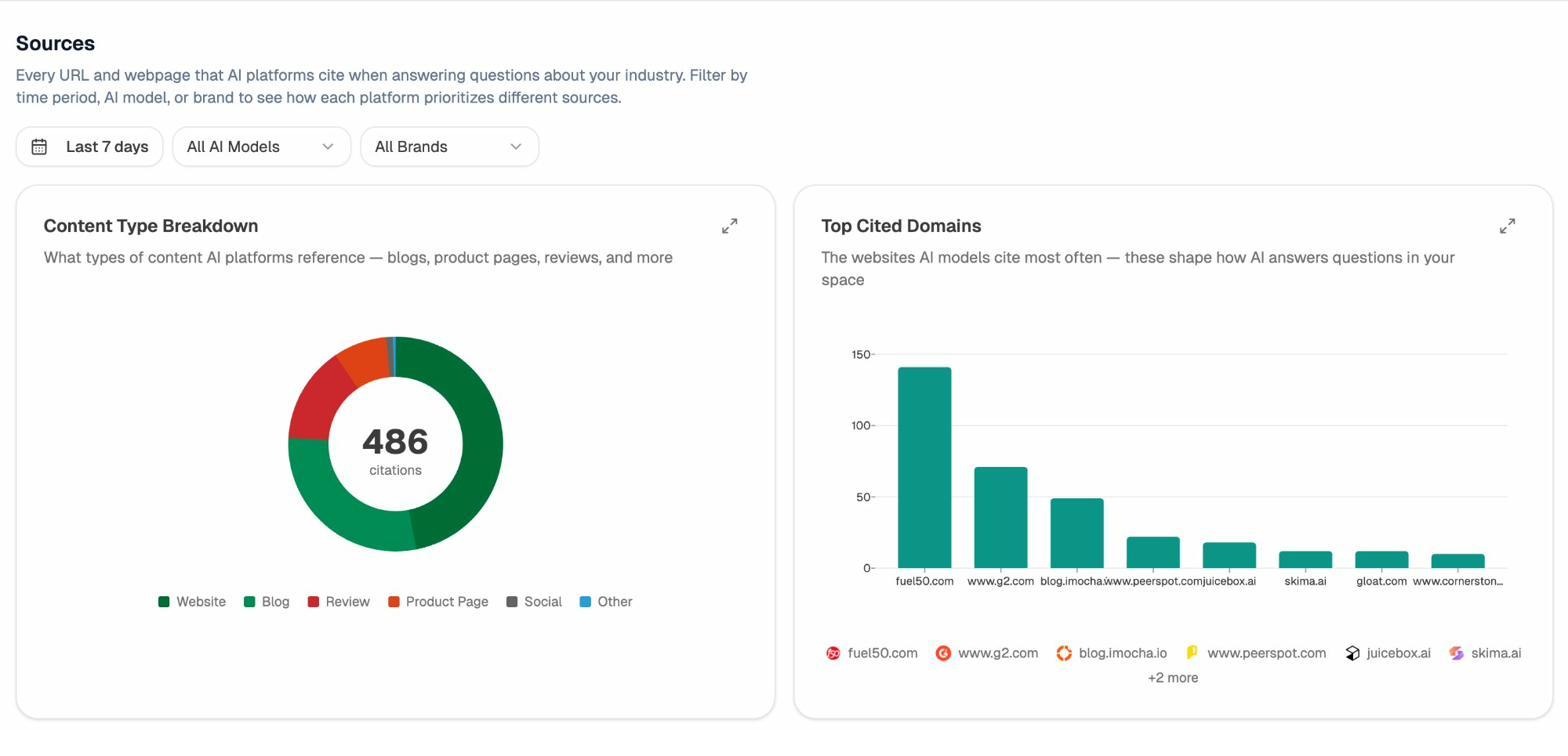
You can track which of your pages AI engines actually cite using a tool like Analyze AI. The Sources dashboard shows every URL that AI platforms reference when answering questions about your industry. If you notice that your HTTP pages are not appearing as citations while competitors’ HTTPS pages are, that is a strong signal to migrate.
Referral Tracking for AI Traffic
Just like with traditional referral data, HTTPS ensures that traffic from AI engines is properly attributed. When ChatGPT or Perplexity links to your page in a citation, that click creates a referral. If your site is on HTTP, that referral data may be lost or misattributed.
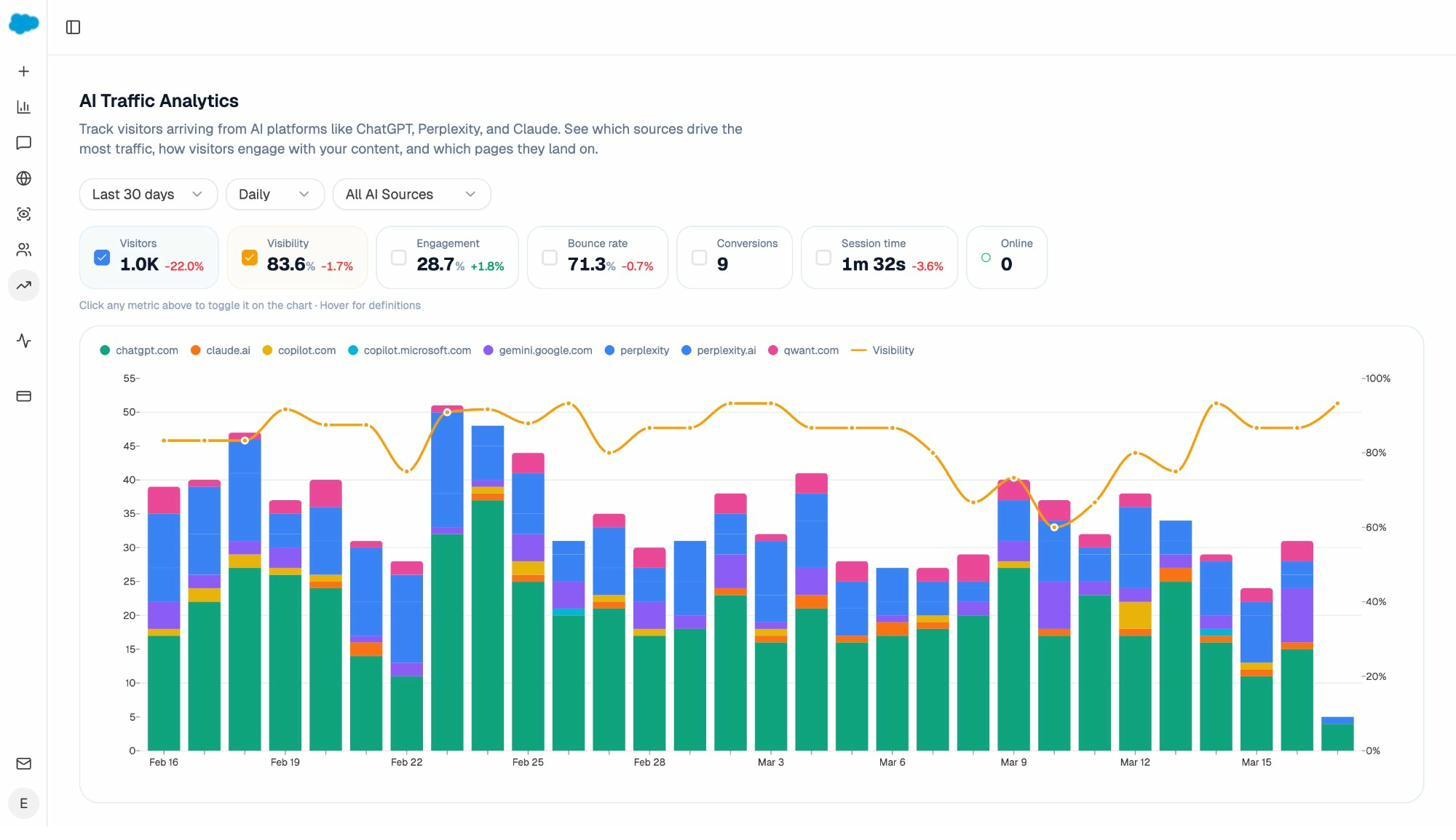
Analyze AI’s AI Traffic Analytics connects to your GA4 data to show exactly which AI engines are sending traffic, which pages they send it to, and how that traffic converts. But this attribution only works cleanly when your site runs on HTTPS.
This is part of a broader shift. SEO is evolving—not dying. AI search is an additional organic channel to optimize alongside traditional search. But the technical foundations remain the same. HTTPS is one of those foundations.
Common HTTPS Errors and How to Fix Them
Before we get into migration, here is a quick reference for the most common HTTPS errors users encounter. If visitors are seeing these errors on your site, fix them immediately—browsers will actively warn people away.
|
Error Code |
What It Means |
Likely Cause |
How to Fix |
|---|---|---|---|
|
NET::ERR_CERT_DATE_INVALID |
The certificate has expired |
Certificate was not renewed on time |
Renew your TLS certificate immediately. Set up auto-renewal if your CA supports it. |
|
NET::ERR_CERT_COMMON_NAME_INVALID |
The domain name does not match the certificate |
Certificate was issued for a different domain, or you added a subdomain not covered by the certificate |
Reissue the certificate with the correct domain name. Consider a wildcard certificate if you use multiple subdomains. |
|
NET::ERR_CERTIFICATE_TRANSPARENCY_REQUIRED |
The certificate is not in Certificate Transparency (CT) logs |
The CA did not log the certificate properly |
Switch to a CT-compliant CA like Let’s Encrypt, DigiCert, or Sectigo. |
|
ERR_SSL_VERSION_OR_CIPHER_MISMATCH |
The browser and server cannot agree on an encryption method |
The server is using outdated TLS versions (1.0 or 1.1) or weak cipher suites |
Enable TLS 1.2 and 1.3 on your server. Disable TLS 1.0 and 1.1 entirely. |
|
Mixed content warning |
The page loads over HTTPS but some resources (images, scripts, CSS) load over HTTP |
Resource URLs in your HTML still use http:// |
Update all resource URLs to https://. Use protocol-relative URLs or absolute HTTPS URLs. |
Most of these errors come from misconfigured servers or certificates that were not renewed in time. The simplest prevention is to use a hosting provider that handles certificate issuance and renewal automatically.
You can also run your site through Analyze AI’s free Broken Link Checker to identify pages with broken resources or mixed content issues. Broken links often accompany HTTPS migration problems, and catching them early prevents a cascade of technical issues.
How to Set Up HTTPS
Your approach depends on where your site stands today.
Scenario 1: You Are Launching a New Website
This is the easiest path. Set up HTTPS from the beginning and you will never have to deal with migration headaches.
Step 1: Choose a hosting provider that includes free TLS certificates. Most modern hosting providers (Cloudflare, Netlify, Vercel, SiteGround, Kinsta) include automatic TLS certificate provisioning through Let’s Encrypt. Confirm this before you sign up.
![[Screenshot: hosting provider dashboard showing automatic SSL/TLS certificate issuance]](https://www.datocms-assets.com/164164/1776444390-blobid8.png)
Step 2: Verify your site loads over HTTPS. After deploying your site, visit it in a browser and confirm the lock icon appears. Test both your root domain (example.com) and any subdomains (www.example.com, blog.example.com).
Step 3: Set up HTTP to HTTPS redirects. Even though your site is HTTPS-only, you need 301 redirects from the HTTP version to the HTTPS version. This ensures that any visitor (or crawler) that tries the HTTP URL gets sent to the right place.
![[Screenshot: server configuration showing 301 redirect from HTTP to HTTPS]](https://www.datocms-assets.com/164164/1776444394-blobid9.png)
Step 4: Implement HSTS. HTTP Strict Transport Security tells browsers to always use HTTPS for your domain, even if someone types http:// in the address bar. This prevents SSL stripping attacks. Add the HSTS header to your server configuration:
Strict-Transport-Security: max-age=31536000; includeSubDomains; preload
Once you are confident everything works, submit your domain to the HSTS Preload List. This hardcodes HTTPS into browsers so they never even attempt an HTTP connection to your site.
Step 5: Verify TLS configuration. Run your domain through Qualys SSL Labs and aim for an A+ rating. Check that TLS 1.3 is enabled and TLS 1.0/1.1 are disabled.
![[Screenshot: Qualys SSL Labs showing an A+ rating with TLS 1.3 and TLS 1.2 only]](https://www.datocms-assets.com/164164/1776444396-blobid10.png)
Scenario 2: You Already Have HTTPS But It May Not Be Configured Correctly
If your site already uses HTTPS but you are not sure it is set up properly, skip to the migration mistakes section below. It covers the five most common errors and how to diagnose each one.
Scenario 3: You Need to Migrate From HTTP to HTTPS
This is the most complex scenario. The difficulty of the migration depends on your site’s size, your CMS, your hosting setup, and your technical skills.
Here is the general process:
Step 1: Get a TLS certificate. If your hosting provider offers free certificates, activate it. If not, purchase one from a CA like DigiCert, Sectigo, or GlobalSign. Choose DV for most sites, OV or EV if you handle payments or sensitive data.
Step 2: Install the certificate on your server. The exact process varies by hosting provider and server software. Your hosting provider’s documentation will walk you through this. Most managed hosting platforms handle installation automatically.
Step 3: Update all internal links to HTTPS. Go through your site’s content, templates, and configuration files. Change every instance of http://yourdomain.com to https://yourdomain.com. This includes links in your navigation, footer, sidebar, and within your content.
Step 4: Update all resource URLs. Images, CSS files, JavaScript files, fonts—any resource loaded by your pages needs to use HTTPS URLs. Missing even one creates a “mixed content” warning.
Step 5: Set up 301 redirects from HTTP to HTTPS. Every HTTP URL on your site should 301 redirect to its HTTPS equivalent. This preserves your existing link equity and ensures search engines update their index.
Step 6: Update your sitemap. Your XML sitemap should list only HTTPS URLs. Submit the updated sitemap to Google Search Console and Bing Webmaster Tools.
Step 7: Update canonical tags. Every page’s canonical tag should point to the HTTPS version. HTTP canonical URLs confuse search engines and dilute your ranking signals.
Step 8: Update your robots.txt. Make sure your robots.txt file references the HTTPS sitemap and does not block any HTTPS URLs.
Step 9: Update external services. Any third-party tools, analytics platforms, social media profiles, or directory listings that link to your HTTP URLs need to be updated. Update your Google Business Profile, social media bios, and email signatures.
Step 10: Monitor for issues. After the migration, use a site audit tool to crawl your site and identify any remaining HTTP references, broken redirects, or mixed content warnings.
![[Screenshot: site audit tool crawl results showing HTTPS migration issues flagged]](https://www.datocms-assets.com/164164/1776444400-blobid11.png)
If this sounds like a lot, that is because it is. For small sites on platforms like WordPress, Shopify, or Squarespace, the process is largely automated. For large or custom-built sites, consider hiring a developer who specializes in site migrations.
How to Check for Potential HTTPS Migration Mistakes
Even after a careful migration, mistakes happen. These five are the most common, and each one can hurt your search performance if left unfixed.
Mistake 1: HTTP Pages Still Exist
The most basic error: some pages on your site still load over HTTP instead of HTTPS.
This usually happens because the redirect rules missed certain URL patterns, or because pages were added after the migration without HTTPS configuration. It also happens with orphaned pages—pages that are not in your sitemap and have no internal links pointing to them. Dedicated PPC landing pages are a common offender.
How to find them:
Crawl your entire site using a site audit tool like Screaming Frog, Sitebulb, or a cloud-based crawler. Make sure the crawler is configured to use all available URL sources: your sitemap, internal links, and any external URL lists (such as PPC landing page URLs from Google Ads).
![[Screenshot: site audit tool configuration showing URL source options — sitemap, crawl, URL list]](https://www.datocms-assets.com/164164/1776444402-blobid12.png)
After the crawl completes, filter for pages serving HTTP status codes. Export that list and set up 301 redirects for each one.
Do not forget PPC landing pages. Export the URL list from your ad platforms (Google Ads, Meta Business Manager) and verify that each one redirects properly to HTTPS. Then update the URLs in your campaign settings to point directly to the HTTPS versions.
Mistake 2: HTTPS Pages Loading HTTP Resources (Mixed Content)
Your page loads over HTTPS, but some of its resources—images, CSS, JavaScript, fonts—still load over HTTP. This is called “mixed content,” and it triggers a browser warning that undermines the trust HTTPS is supposed to provide.
Mixed content comes in two flavors. “Active” mixed content (scripts, iframes) is blocked entirely by modern browsers, which can break page functionality. “Passive” mixed content (images, video, audio) may load but triggers a console warning and removes the lock icon.
How to find it:
Open your browser’s developer tools (F12), go to the Console tab, and look for mixed content warnings. For a site-wide check, use a crawler that flags mixed content issues.
![[Screenshot: browser developer console showing mixed content warnings for HTTP resources]](https://www.datocms-assets.com/164164/1776444406-blobid13.jpg)
How to fix it:
Update every resource URL to use HTTPS. In most cases, this means changing http:// to https:// in your templates, CMS settings, and content. If a third-party resource does not support HTTPS, find an alternative that does or host the resource yourself.
A quick find-and-replace in your database can handle bulk updates. On WordPress, plugins like Better Search Replace make this straightforward. For custom sites, a simple sed command or database query will do the job.
Mistake 3: Internal Links Still Pointing to HTTP
If your internal links still use HTTP URLs, every click triggers an unnecessary redirect. The redirect works—the visitor ends up on the HTTPS page—but the extra hop wastes crawl budget and adds latency.
How to find them:
Run a site crawl and filter for internal links with HTTP destinations. Most crawlers flag this as a warning.
![[Screenshot: site audit report showing internal links pointing to HTTP URLs]](https://www.datocms-assets.com/164164/1776444408-blobid14.png)
How to fix them:
Rewrite the link URLs to use https://. This is safe to do only after confirming that no HTTP-only pages remain (Mistake 1). If HTTP pages still exist, fix those first—otherwise you will create broken links.
On large sites, use your CMS’s search-and-replace functionality or a database query to update all internal link URLs at once.
Mistake 4: Canonical and Open Graph Tags Still Using HTTP
Two types of meta tags frequently get overlooked during HTTPS migrations: canonical tags and Open Graph tags.
Canonical tags tell search engines which version of a page is the “official” one. If your canonical tag points to http://example.com/page while the page itself loads at https://example.com/page, you are telling Google that the HTTP version is authoritative. Google will likely ignore this signal, but it creates confusion in your crawl reports and wastes search engine resources.
Open Graph tags control how your pages appear when shared on Facebook, LinkedIn, and other social platforms. The og:url tag must match your canonical URL. If it points to HTTP, your social shares may not display correctly.
How to find them:
Use a crawler to check the canonical and OG URL tags across your site. Filter for any pages where these tags contain http:// URLs.
![[Screenshot: site audit tool showing pages with HTTP canonical tags highlighted]](https://www.datocms-assets.com/164164/1776444412-blobid15.png)
How to fix them:
Update the canonical and OG URL tags to use https://. In most CMS platforms, this is controlled by a site-wide setting. In WordPress, updating the site URL in Settings > General typically fixes canonical tags automatically. OG tags may require a plugin update or template edit.
Mistake 5: Redirect Chains and Broken Redirects
Redirects are where HTTPS migrations most commonly go wrong. The three most common redirect issues:
Redirect chains: A URL redirects to another URL, which redirects to yet another URL. For example: http://example.com → https://example.com → https://www.example.com. Each hop adds latency and wastes crawl budget. Search engines will follow redirect chains, but they prefer direct paths.
Redirect loops: A URL redirects to another URL, which redirects back to the first one. The browser gives up and shows an error. This completely blocks access to the page.
Broken redirects: A redirect points to a URL that returns a 404 or 5xx error. The visitor reaches a dead end.
How to find them:
Run a full site crawl with redirect tracing enabled. The crawler will flag redirect chains (more than one hop), redirect loops, and redirects that lead to error pages.
![[Screenshot: site audit tool showing redirect chain details with each hop visualized]](https://www.datocms-assets.com/164164/1776444414-blobid16.png)
How to fix them:
For redirect chains, update each redirect to point directly to the final destination URL. If http://example.com currently redirects to https://example.com, which then redirects to https://www.example.com, change the first redirect to go directly to https://www.example.com.
For redirect loops, identify which redirect rule is creating the loop and remove or correct it. This usually happens when competing redirect rules conflict—for example, one rule redirects HTTP to HTTPS and another redirects non-www to www, but they interact in unexpected ways.
For broken redirects, either fix the destination URL or update the redirect to point to a valid page.
After fixing redirects, also update any internal links that point to the old (redirected) URLs. This eliminates the redirect entirely for internal traffic and sends a cleaner signal to search engines.
The HTTPS Checklist for AI Search Readiness
Beyond the standard SEO benefits, ensuring your HTTPS setup is solid positions your site for maximum visibility in AI search results. Here is a condensed checklist that covers both traditional and AI search considerations.
Technical foundations: - TLS certificate is valid and auto-renewing - TLS 1.3 is enabled with TLS 1.2 fallback - TLS 1.0 and 1.1 are disabled - HTTP to HTTPS 301 redirects are in place for all URLs - HSTS header is configured and domain is on the HSTS preload list - No mixed content warnings across any page - All internal links use HTTPS URLs - Canonical tags and OG tags point to HTTPS URLs - XML sitemap contains only HTTPS URLs - robots.txt does not block HTTPS pages
AI search readiness: - Verify that AI crawlers (GPTBot, ClaudeBot, PerplexityBot, Google-Extended) are not blocked in robots.txt - Confirm your HTTPS pages are accessible to AI crawlers by checking server logs - Monitor which of your pages are being cited by AI engines using Analyze AI’s Sources dashboard - Track AI referral traffic to identify which pages receive visits from AI-generated citations - Compare your AI citation rate against competitors to spot gaps
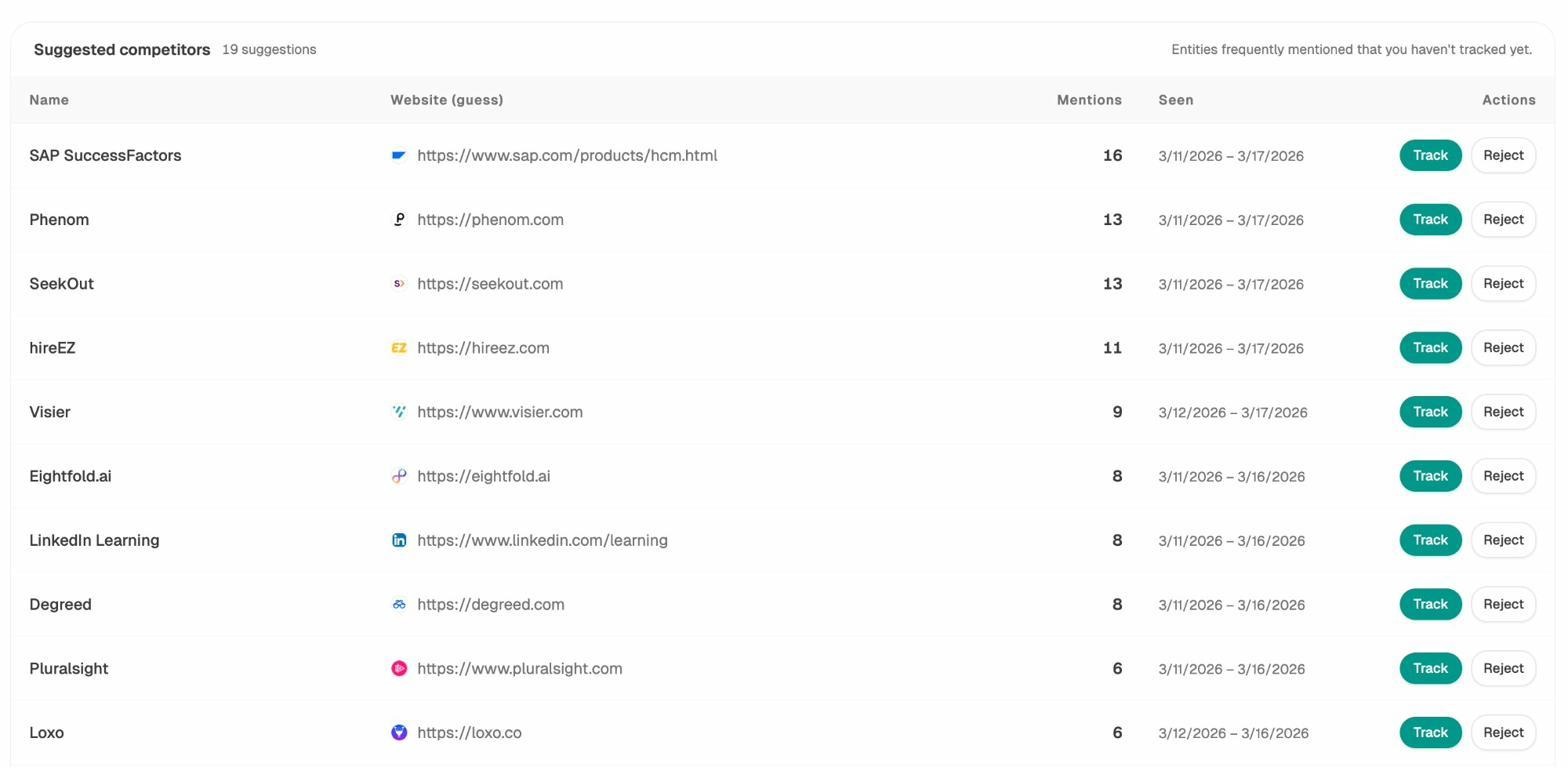
If you are not yet tracking your AI search presence, this is a good time to start. Analyze AI monitors how your brand appears across ChatGPT, Perplexity, Claude, Gemini, and Copilot. It shows which prompts trigger mentions of your brand, which competitors appear alongside you, and which of your pages get cited most often.
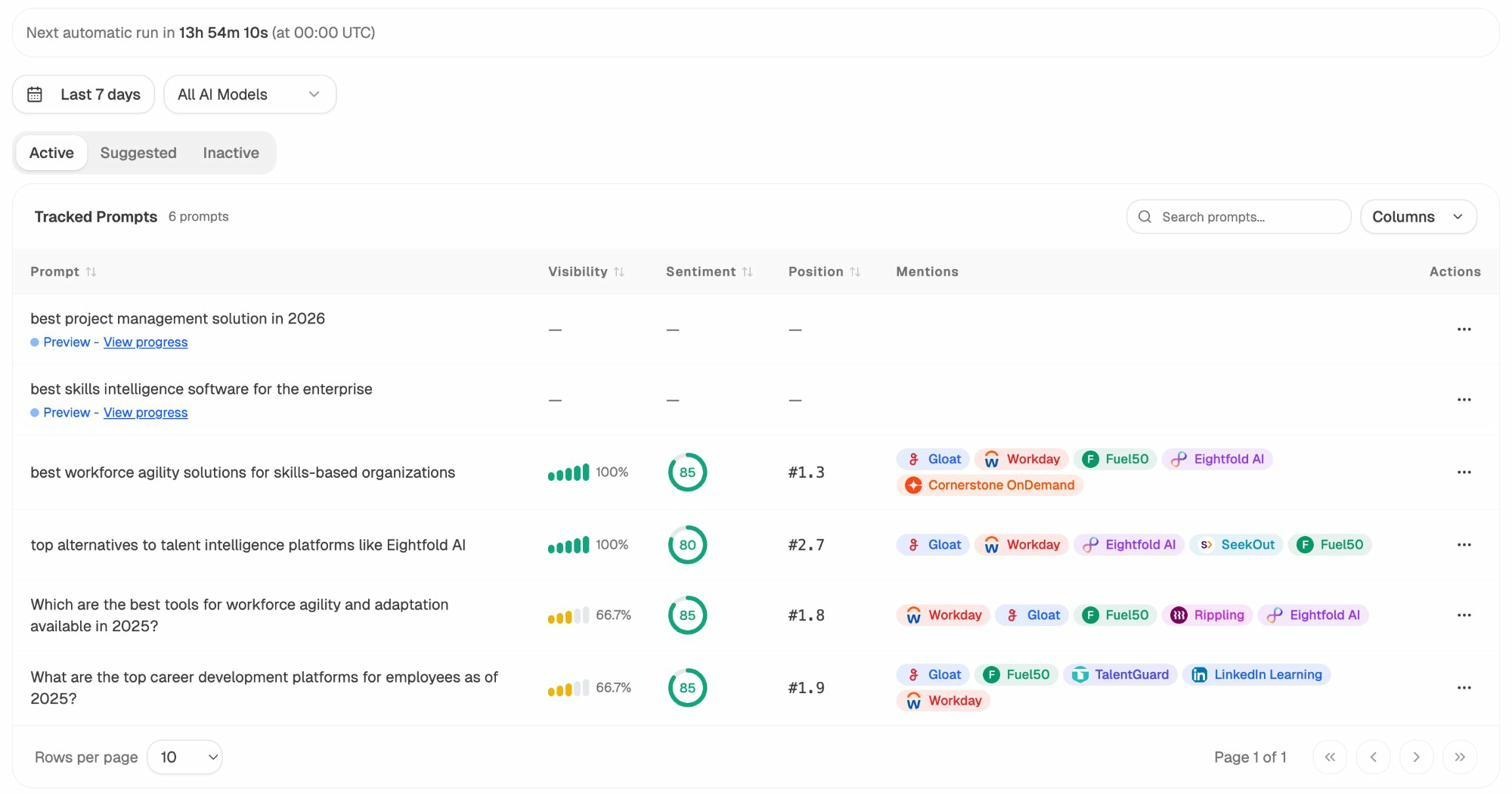
This data is useful for answer engine optimization (AEO)—a discipline that sits alongside traditional SEO. While traditional SEO focuses on ranking in Google’s organic results, AEO focuses on getting cited in AI-generated answers. Both channels benefit from the same technical foundations, and HTTPS is one of the most fundamental.
HSTS: The Final Layer of HTTPS Security
We mentioned HSTS earlier, but it deserves its own section because it is frequently skipped—and skipping it leaves a real vulnerability.
HTTP Strict Transport Security (HSTS) is an HTTP response header that tells browsers: “Only connect to this site using HTTPS. Do not attempt HTTP connections. Ever.”
Without HSTS, a browser might still attempt an HTTP connection on the first visit before being redirected to HTTPS. That brief moment of HTTP is enough for an attacker to intercept the connection (SSL stripping attack).
With HSTS, the browser knows before making any request that it should only use HTTPS. After the first visit (where the HSTS header is received), the browser never attempts HTTP again for the duration specified in the max-age directive.
How to Implement HSTS
Add this header to your server’s response:
Strict-Transport-Security: max-age=31536000; includeSubDomains; preload
Here is what each directive means:
-
max-age=31536000: The browser should remember this rule for one year (31,536,000 seconds).
-
includeSubDomains: Apply the rule to all subdomains too.
-
preload: Signals that you want to be added to the browser’s built-in HSTS preload list.
The HSTS Preload List
The HSTS header only takes effect after a browser has visited your site at least once. The preload list eliminates even that first HTTP request. When your domain is on the preload list, browsers like Chrome, Firefox, Safari, and Edge know to use HTTPS before they ever contact your server.
To get on the preload list:
-
Serve a valid HSTS header with max-age of at least one year, includeSubDomains, and preload.
-
Redirect all HTTP requests to HTTPS on the same host.
-
Serve all subdomains over HTTPS.
-
Submit your domain at hstspreload.org.
Warning: Getting on the preload list is easy. Getting off it is hard. If you submit your domain and later decide to serve some subdomains over HTTP, you will have a problem. Only submit once you are confident that every subdomain will remain on HTTPS permanently.
Certificate Automation: Let’s Encrypt and ACME
Manual certificate management is a recipe for expired certificates and downtime. Automation solves this.
Let’s Encrypt is a free, nonprofit Certificate Authority that has fundamentally changed how the web handles TLS certificates. Before Let’s Encrypt launched in 2016, getting a TLS certificate required paying a CA, waiting for verification, and manually installing the certificate. Let’s Encrypt made the process free and automatic.
The key technology behind this automation is the ACME protocol (Automatic Certificate Management Environment). ACME allows software on your server to request, validate, and renew certificates without human intervention.
Most modern hosting providers use ACME behind the scenes. If your hosting provider offers “free SSL” or “automatic HTTPS,” they are almost certainly using Let’s Encrypt and ACME.
How Auto-Renewal Works
Let’s Encrypt certificates are valid for 90 days. This short lifespan is intentional—it encourages automation and limits the damage if a certificate’s private key is compromised.
With ACME-based tools like Certbot, your server automatically requests a new certificate before the current one expires. The process runs in the background without any manual intervention.
If you manage your own server, install Certbot and set up a cron job for renewal:
# Test renewal
sudo certbot renew --dry-run
# The actual renewal runs automatically via systemd or cron
If you use a managed hosting provider or CDN like Cloudflare, certificate renewal is handled for you. Just verify that auto-renewal is enabled in your dashboard.
![[Screenshot: hosting provider dashboard showing auto-renewal status for TLS certificate]](https://www.datocms-assets.com/164164/1776444424-blobid19.png)
Testing Your HTTPS Configuration
After setting up HTTPS or completing a migration, test everything. Here are the tools and checks that matter.
External Testing Tools
Qualys SSL Labs: The industry standard for testing TLS configuration. It checks your certificate, protocol support, key exchange, and cipher strength. Aim for an A+ rating.
![[Screenshot: Qualys SSL Labs test result page showing protocol support and cipher details]](https://www.datocms-assets.com/164164/1776444425-blobid20.png)
Mozilla Observatory: Tests security headers beyond just TLS—including HSTS, Content Security Policy, X-Frame-Options, and more. A useful complement to SSL Labs.
Security Headers: Focused specifically on HTTP security headers. Useful for verifying HSTS, CSP, and other protective headers.
Manual Checks
Check for mixed content: Open your browser’s developer tools (F12), load your page, and check the Console tab for mixed content warnings.
Verify redirects: Use curl to check that HTTP URLs redirect properly:
curl -I http://yourdomain.com
You should see a 301 Moved Permanently status with a Location header pointing to the HTTPS URL.
Check certificate details: Click the lock icon in your browser and verify the certificate’s validity dates, issuer, and domain coverage.
Ongoing Monitoring
HTTPS configuration is not a one-time task. Certificates expire, server configurations change, and new content can introduce mixed content issues. Set up ongoing monitoring to catch problems before they affect visitors.
Use your analytics platform to watch for sudden traffic drops after certificate-related changes. And use a site monitoring tool to get alerted when your certificate is about to expire or when your TLS configuration degrades.
You can use Analyze AI’s free Website Traffic Checker to monitor traffic patterns. A sudden drop in organic traffic after an HTTPS change is often the first sign of a migration issue. Similarly, if you notice a drop in AI referral traffic in Analyze AI’s AI Traffic Analytics, it could indicate that AI crawlers are encountering HTTPS errors on your site.
Frequently Asked Questions About HTTPS
Does HTTPS slow down my site?
No. The encryption overhead is negligible on modern hardware. And HTTPS is required for HTTP/2 and HTTP/3, which make your site faster than it could ever be on HTTP/1.1.
Is a free TLS certificate as secure as a paid one?
Yes. From a technical security standpoint, a free DV certificate from Let’s Encrypt provides the same encryption strength as a paid certificate. The difference is in the validation level (DV vs. OV vs. EV), not the encryption quality.
Do I need HTTPS if my site does not collect any data?
Yes. HTTPS protects your visitors from content injection, prevents ISPs from inserting ads into your pages, preserves referral data in analytics, and is a Google ranking signal. There is no valid reason to run any public website on HTTP in 2026.
What happens to my SEO rankings during an HTTPS migration?
Temporary fluctuations are normal. Google needs to recrawl and reindex your pages under the new URLs. If the migration is done correctly with proper 301 redirects, your rankings should stabilize within a few weeks. If rankings drop significantly and do not recover, check for the migration mistakes listed above.
Do AI search engines care about HTTPS?
AI engines like ChatGPT, Perplexity, and Gemini rely on web crawlers that follow similar protocols to search engine crawlers. HTTPS is a trust signal that can influence whether your content gets indexed and cited. While no AI engine has explicitly stated HTTPS as a ranking factor, the correlation between site trustworthiness and AI citation rates is well-documented.
You can track your AI search visibility with Analyze AI to see how your brand appears across AI platforms and whether your pages are being cited.
How do I check if my HTTPS is set up correctly?
Run your domain through Qualys SSL Labs for a comprehensive TLS check, then use Mozilla Observatory for broader security header analysis. You can also check for broken links and mixed content with Analyze AI’s Broken Link Checker.
Final Thoughts
HTTPS is a non-negotiable technical foundation for any website in 2026. It protects your visitors, preserves your analytics data, enables faster page loads through modern protocols, and sends a positive trust signal to both Google and AI search engines.
With Chrome’s HTTPS-by-default rollout approaching later this year, the urgency is real. Sites that still run on HTTP will face active warnings that drive visitors away.
If you are launching a new site, start with HTTPS from day one. If you are migrating, follow the steps above and check for the five common mistakes. And if you want to understand how your HTTPS pages are performing not just in Google but across AI search engines, Analyze AI can show you which pages AI engines cite, which competitors they recommend instead, and where your gaps are.
The web is moving toward encrypted-by-default. Make sure your site is ready.
Ernest
Ibrahim







